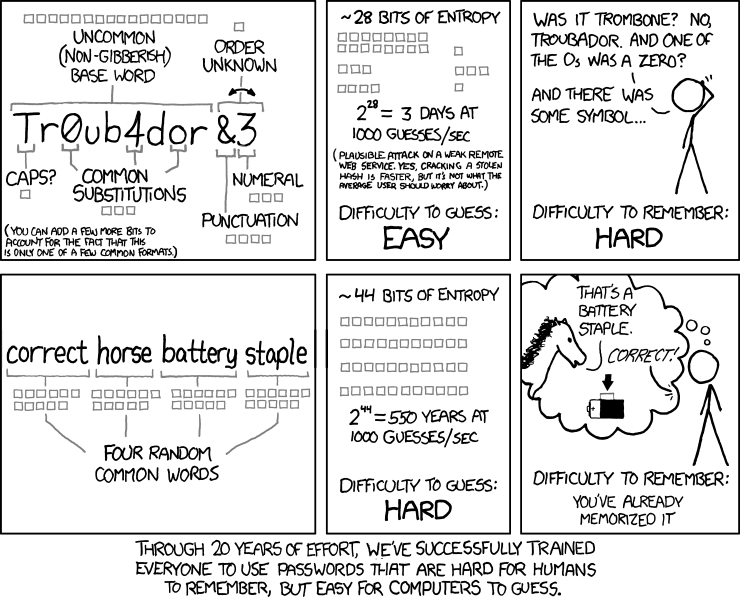
Why have we been relying so heavily on SMS to provide us with extra security when SMS itself is not secure? Gmail, Facebook, Twitter, Apple, PayPal, even LastPass (my chosen password manager) among a majority of other services we use daily offer two-factor authentication (2FA) via SMS. The only service I use that does not provide an SMS option for its 2FA is ProtonMail. There is a very good reason a service built on security does not have this option. While LastPass does provide the option, it discourages it in favour of an authentication app. Let me preface this by saying SMS-based 2FA is better than no 2FA at all. We will get to that later.
SMS is an outdated service; we have much more secure messaging services such as iMessage, WhatsApp, etc. SMS messages are unencrypted and pass through multiple unsecured networks. This means that your mobile carrier, the government and hackers can read the contents of your messages. Another basic security flaw is due to the fact that while our phones and other devices are generally protected through biometrics or a password, our SIM cards are not (although some people do use passwords for theirs). Someone with access to your phone can use your SIM card by simply putting it in their own device. Then there are also SIM swap attacks. Attackers can socially engineer the victim to then use this information to convince an employee of their phone service provider to port their number to a SIM held by the attacker. Of course, in most security systems, the human factor is the weakest link. Employees can also simply be bribed to port the victim’s phone number.
But please do not forego 2FA altogether! A relatively easy to overcome hurdle is still an extra hurdle. Attackers generally tend to choose the easier, quicker option so those without 2FA become victims more often. Please also do not make the mistake of thinking that your accounts are not worth hacking or that hackers will not find anything of use in your accounts. Everyone should use 2FA, even if it is SMS based. With that said, if you’re ready to ditch SMS as your method of 2FA, here are some app options:
- Authy
- FreeOTP (open source)
- Duo Mobile
- Microsoft Authenticator [Google Play] [App Store]
- Google Authenticator [Google Play] [App Store]
If you seek even more security or less hassle, you can go with a hardware-based solution (Universal 2nd Factor) which involves physically using a key. Yep, it’s a little ironic. Here are Yubico and Google’s Universal 2nd Factor (U2F) options: